Cybercrime experts warn of ways in which criminals are preying on the technological vulnerabilities brought on by the current Coronavirus pandemic. Scammers seek to exploit individuals by contacting them about alarming matters such as COVID-19 testing, donation requests, financial assistance for victims of the Coronavirus and high-demand supplies related to the pandemic.
Unfortunately, many people fall victim to these scams. Money is stolen. Personal identities and passwords are stolen. Many times, malware is installed on private computer systems; compromising the security of not only that system, but also infecting the systems they are in contact with. Just like the Coronavirus, malware can be contagious and spread like wildfire. All this during a time when many people are most vulnerable.
Cyber insurance can help protect your business if you or your employees fall victim to these scams, which are constantly becoming more sophisticated. In addition to cyber insurance, below are some of the types of COVID-19 scams that have become problematic in addition to some red flags to look out for.
Types of COVID-19 Scams
Smishing
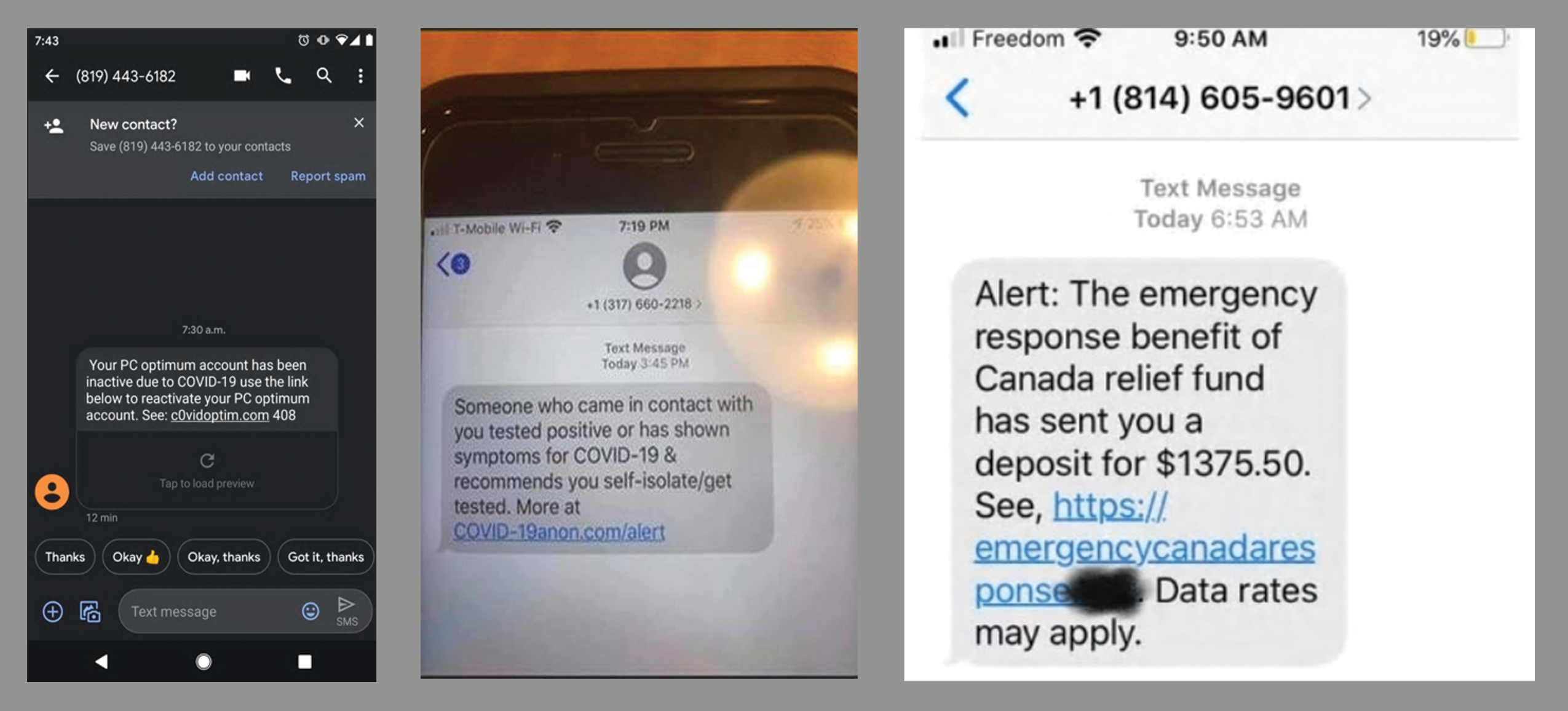
Smishing is a form of social engineering that exploits victims by using SMS, or text messages. This integration of email, voice, text message, and web browser functionality increases the likelihood that users will fall victim to engineered malicious activity.
Text messages can contain links to webpages, email addresses or phone numbers. Once clicked on, it may automatically open a browser window or email message or dial a number. This act alone can trigger malware to be downloaded!
Scammers take advantage of individuals by using alarming messages such as:
- "Someone who came in contact with you tested positive or has shown symptoms for COVID-19 & recommends you self-isolate/get tested. More at <malicious link>"
- "Alert: The emergency response benefit of Canada relief fund has sent you a deposit for $1375.50. See, <malicious link>. Data rates may apply."
Vishing
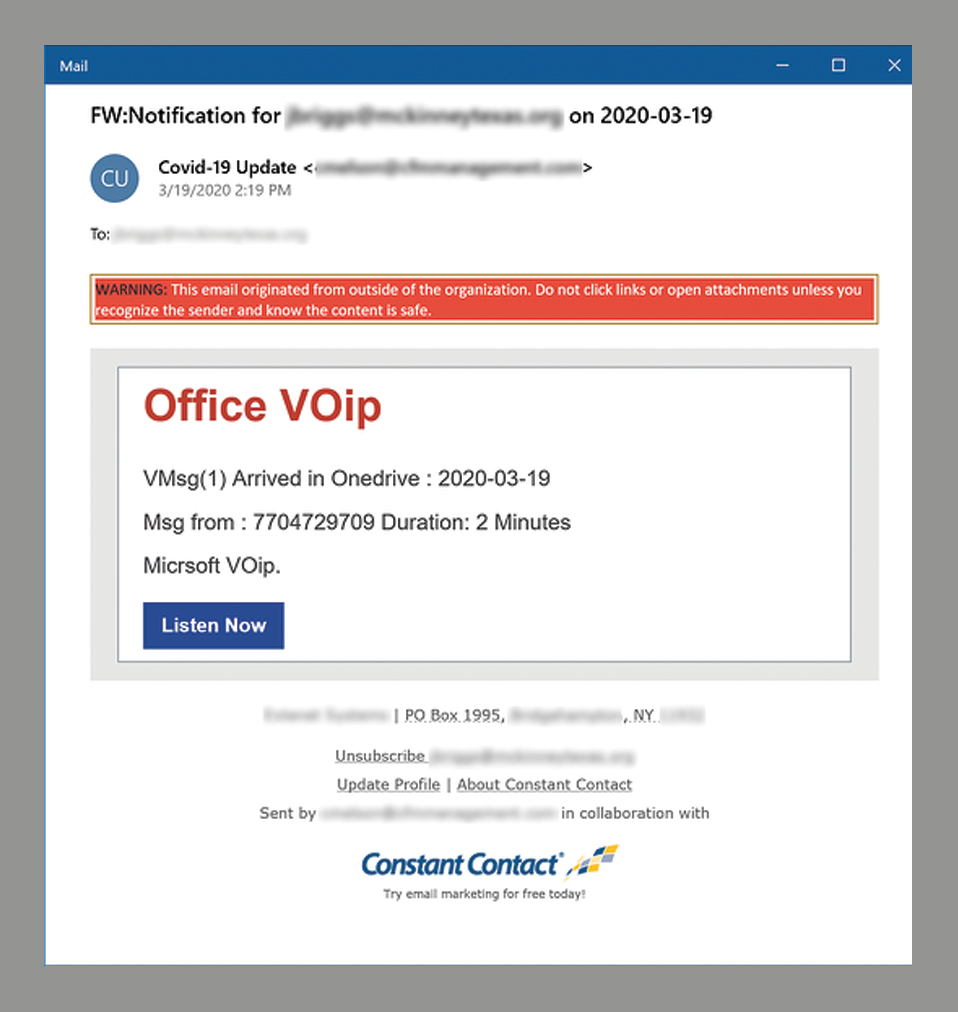
Vishing is the social engineering approach that uses voice communication. This approach can be combined with other social engineering methods that entice victims to call certain numbers and give out sensitive, personal information.
Advanced vishing attacks can take place completely over voice communications by exploiting Voice over Internet Protocol (VoIP) and broadcasting services. VoIP easily allows caller identity to be faked, taking advantage of the public’s misplaced trust in the security of phone services, especially landline services. Although landline communication cannot be intercepted without physical access to the line; this feature is not beneficial when communicating directly with a scammer.
An example of a vishing attempt is an email that appears to come from your VoIP provider and appears to contain a voicemail message which you need to click a "Listen Now" button to access. This button contains a malicious link.
Phishing
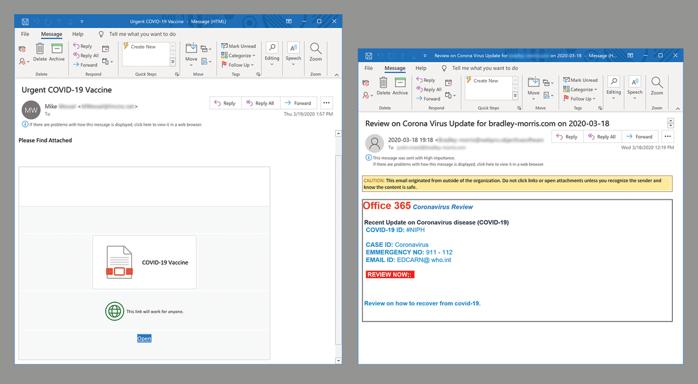
Phishing is another form of social engineering used most frequently. According to Google, phishing scams have increased 350% since January 1st. Phishing attacks use email or malicious websites to solicit personal information by posing as a trustworthy organization.
For example, an attacker may send email seemingly from a reputable financial institution that requests account information, often suggesting that there is a problem. When users respond with the requested information, attackers can use it to gain access to the accounts.
Phishing attacks may also appear to come from other types of organizations, such as charities, government entities, and more. Attackers often take advantage of current events and certain times of the year:
- Natural disasters (e.g., Hurricane Katrina)
- Epidemics and health concerns (e.g., H1N1, COVID-19)
- Economic concerns (e.g., IRS scams)
- Political elections
- Holidays
Red Flags to Look out For
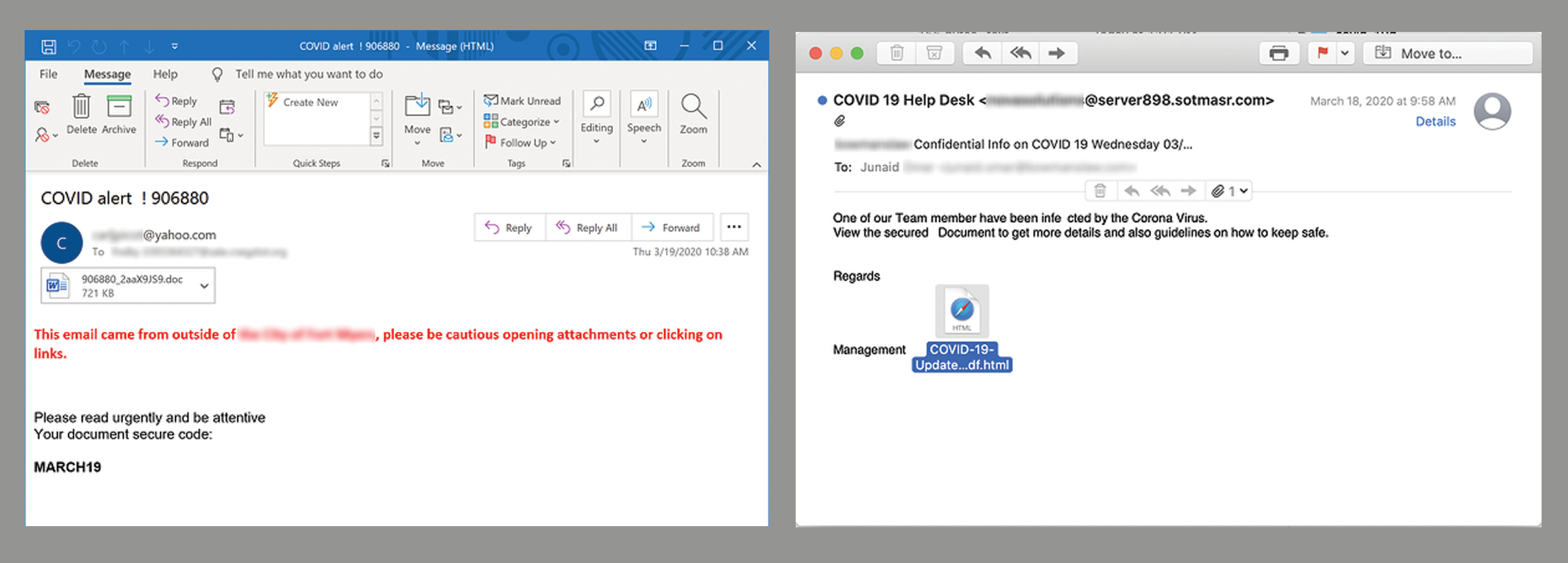
- Suspicious mail addresses. The sender's email address may appear legitimate because cybercriminals typically use email addresses that resemble those of reputable companies. Characters within the email addresses are changed or omitted which, can easily be overlooked.
- Generic greetings and signature. Generic greetings like “Dear Valued Customer” or “Sir/Ma’am” and lack of contact information in signatures
are good indicators of a phishing. Trusted organizations will provide their contact information and address you by name. - Spelling and layout. Poor grammar and incomplete sentence structure and misspellings can also be indicators of a phishing attempt.
- Suspicious attachments. Unsolicited emails requesting a user download or opening attachments is a common delivery mechanism for malware. Cybercriminals use a false sense of urgency to persuade victims to do what they request.
- Spoofed hyperlinks and websites. If you hover your cursor over a link in the body of an email, but the link doesn't match the text that appears when hovering over them, the link may be spoofed. Malicious websites may look identical to a legitimate site, but the URL may have a spelling variation or a different domain altogether. Additionally, URLs can be shortened to hide the true destination of the link.
Some examples include:
- Email with subject line "Urgent COVID-19 Vaccine" that contains a malicious attachment you must open to access information on the "vaccine."
- Email with subject line "Review on Corona Virus Update" appearing to come from Office 365 Coronavirus Review. To review how to recover from COVID-19, you must click on a malicious link.
- Email with subject line "COVID alert" asking the user to "Please read urgently and be attentive." The email provides a "document secure code" and a Word document is attached. When opened, this Word document could deliver malware.
- Email with subject line "COVID 19 Help Desk" appearing to come from your HR department. When you look closer at the sender address, you can see that it is a suspicious email address. The body of the email states "One of our Team member have been finected by the Corona Virus. View the secured Document to get more details and also guidelines on how to keep safe." You notice some typos in the message, and the sign-off is "Management." A malicious link is included in the email.
How Cyber Insurance Can Help
Cyber insurance is a specialized form of insurance that is designed to protect businesses from online threats and the risks that potential data breaches pose. You should work closely with an insurance agent to find a cyber policy that offers robust protection against these threats.
As an independent agent who is familiar with this form of insurance, we have the ability to request quotes from multiple insurers to find the best mix of protection and price to fit your unique needs, and we will be able to accurately compare each policy's coverages for you.
If you are interested in learning more about cyber insurance or obtaining a quote, please give us a call at 732-380-0900 or visit our cyber insurance page.
The information contained here is for informational purposes only and not for the purpose of providing legal advice. Individuals and businesses should consult with their attorney to obtain advice regarding their specific situation.
Get Started with a Free consultation
Creating a custom insurance or benefits package is critical for companies of all sizes.